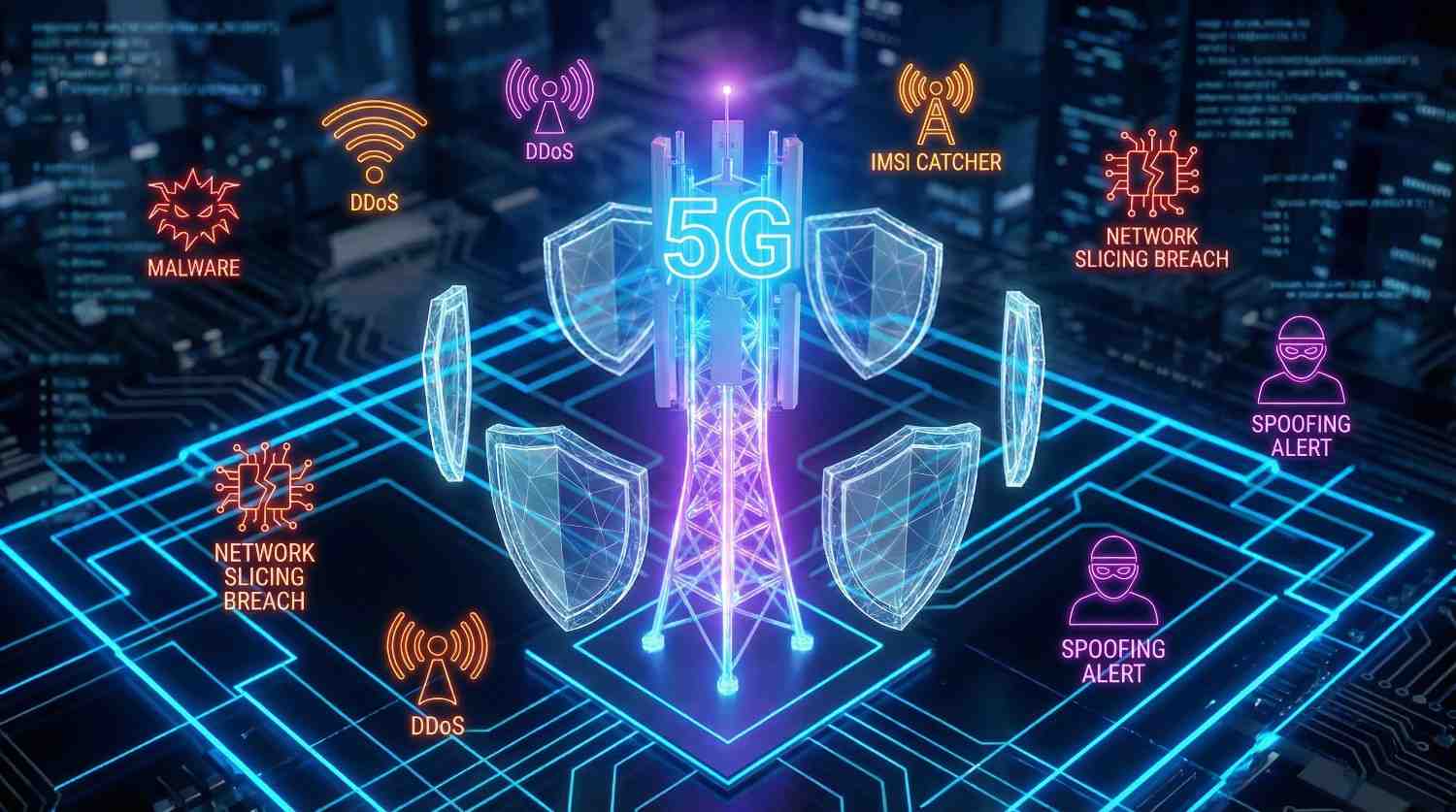
5G: Power, Fragility, and the Future of Network Security
Souvik Karmakar
24th November 2025
5G feels both powerful and fragile when it begins to move ahead. It opens speed, connection, and change while it invites threat, complexity, and doubt together. Every new device connects a world where trust must be adapted carefully. Every signal carries promise and risk when technology continues to evolve. Security now walks beside innovation as it learns to adapt quickly, and both move fast to catch balance.
How Is 5G Changing Network Security?
What Makes 5G Different From 4G and LTE?
5G builds with software, not only hardware, and it moves with quiet precision. It runs through clouds and edges where it seeks a faster reach. It moves data with intent and design while maintaining stability. It replaces control with flexibility, and it stretches distance into speed through structure. Unlike 4G, it breathes through many layers that continue to grow. These layers bring freedom and risk as they expand, and they widen the field for attack where defense must hold.
Why Does 5G’s Design Increase Risk Exposure?
Every open path carries exposure when a system grows wide. Each new virtual link becomes a door that someone can test quietly. When code replaces circuits, mistakes become silent holes in waiting. A single missed update may open a breach that grows unseen. In 5G, the map is vast and living, and the danger hides in the details that shift often.
What Are the Main 5G Security Risks?
How Does 5G Expand the Attack Surface?
With 5G, the surface grows without end while the world connects faster. Billions of IoT devices connect and speak, and they form endless signals. Each one asks for trust and constant validation. Some fail to earn it and invite a threat. A camera, a sensor, or a car may fall first before another, and a network may fall next in silence.
Why Are IoT Devices Prime Targets?
IoT devices are simple and exposed when they reach the field. They often forget encryption as they focus on speed. They skip updates and share weak passwords with careless design. Attackers look for easy entry where patience pays, and they find it in these tiny machines that hold power. A small mistake there can cause great harm here when it spreads quickly.
Can Network Slicing Create New Threats?
Network slicing divides a single system into many private lanes that require control. It helps businesses, healthcare, and transport move separately and securely with ease. Yet separation needs constant watch as it changes daily. If one slice leaks, the rest may follow soon after without warning.
How Can Hackers Exploit 5G Slices?
A hacker may enter through a weak slice when it opens quietly. They may cross between layers through flawed isolation that fails slowly. If controls fail, one attack spreads quietly and deeply. Security here depends on a sharp design that never rests, and it must never sleep or drift.
What Are the Supply Chain Vulnerabilities?
Every network depends on what it buys, and it grows through shared trust. Hardware and code come from many hands that build and deliver parts. If one link breaks trust, all others tremble and weaken further. A chip can hide a flaw that nobody detects soon. A supplier can slip a door when attention fades away. A system that trusts too easily soon regrets deeply because danger waits quietly.
How Can Third-Party Vendors Compromise 5G Security?
Third-party vendors add scale and reach, but they also add risk each day. They may use outdated software that stays hidden inside. They may skip security testing and delay vital reviews. Attackers move where rules feel weak and unsure. The supply chain needs proof and review, not blind belief that fades over time.
Is Edge Computing a Security Weak Spot?
Edge computing sits close to users where speed matters most. It carries data near the source, and it works under pressure. It speeds response and lowers strain for connected systems. Yet it divides protection and spreads defense thinly. Each edge node must defend itself with care. When one fails, data may leak before reaching the core as attacks grow.
What Happens When Data Is Processed at the Edge?
When data moves through local edges, it becomes light but exposed often. Attackers aim for small servers that handle vital information. They blend in with normal traffic and stay hidden quietly. Once they enter, they watch and wait before acting. Edge computing demands constant care and clean isolation that stays strong.
How Do Identity and Authentication Issues Arise?
Each connected device must prove its name and integrity. In 5G, names are endless and scattered widely. Machines talk faster than humans can track when networks expand. Weak authentication becomes a crack in trust that spreads easily. One fake identity can fool a system built for billions without notice.
Why Is Device Identity Hard to Manage in 5G?
IoT devices are small and cheap when produced in volume. Many lack the memory or power to encrypt data well enough. Managing secure identity takes energy and attention each day. The system must balance safety with function carefully. That balance remains fragile and thin under pressure.
How Does 5G Impact IoT Device Security?
Why Does 5G Increase IoT Connectivity Risks?
5G invites everything to connect at once, and it grows vast. Homes, farms, and factories breathe through it daily. With each connection, the network grows more alive and aware. It also grows more vulnerable and reactive to attack. One weak node can echo trouble across a city before dawn.
What Common Flaws Exist in IoT Security?
The flaws often sound simple and clear. Old firmware, weak keys, exposed APIs, and careless design often return. Yet simple mistakes cause complex failures that surprise many. Attackers love these small doors and wait patiently. They walk in where attention fades, and they stay long unseen.
How Can Smart Cities and Industries Stay Secure?
Smart cities must build layers of defense with purpose. Devices must encrypt and verify their data carefully. Systems must log and audit behavior across environments. Updates must reach on time and with care. Industrial networks must isolate their core and protect the flow. Security is not an act; it is a habit learned deeply.
Why Is Critical Infrastructure at Risk?
How Does 5G Integrate With Power, Transport, and Health Systems?
5G sits inside every pulse of modern life that depends on flow. It carries energy data, medical signals, and transport control safely. When it works, cities move with grace and rhythm. When it fails, silence spreads fast through systems. The link between digital and physical grows closer, and that closeness brings danger and tension.
What Could Go Wrong in a Cyberattack?
A 5G breach could stop a hospital machine instantly. It could misguide a grid or delay an ambulance response entirely. Attacks no longer steal only data or cause delay. They now touch real lives and change outcomes. The threat is not abstract or distant; it breathes among us.
Is There a Geopolitical Side to 5G Security?
Yes, and it runs deep beneath systems. Nations worry about the control and influence that shape policy. Equipment comes from foreign makers who compete for trust. Governments seek trust where politics stir doubt and noise. 5G is not only technology, it is power wrapped in signal and code.
How Can We Secure 5G Networks?
What Are the Best Practices for Network Design?
Security must begin before design ends, and it must grow together. It must live inside the architecture where choices matter most. Encryption must guard every layer and each link carefully. Monitoring must never rest, and awareness must spread. Trust must be tested daily with intent. A strong 5G network grows from discipline and review that stay active.
How Does Network Slicing Isolation Help?
Each network slice should stay alone with strict control. Isolation keeps one breach from reaching others when trouble starts. Boundaries must be strict and enforced fully. Separation becomes safety when built with care and attention.
Why Is Continuous Monitoring Crucial?
Threats evolve faster than rules can adjust fully. Continuous monitoring catches motion, not memory, and learns. It finds the whisper before the shout begins. Networks that watch survive longer than networks that wait or pause.
What Is a Zero-Trust Model for 5G?
Zero trust means verify everything every time. It means doubt by design, and protection through proof. It means that even friends must prove who they are always. In 5G, this mindset fits well and deepens defense. It shrinks the space where attackers hide and wait.
How Does AI Help Detect Threats in Real Time?
AI listens where humans tire quickly. It reads traffic, patterns, and intent through layers. It finds noise that feels wrong and subtle. It acts before humans can think or react. Machine learning grows with data and time, and defense grows with it always.
Which Standards and Regulations Apply?
Frameworks like 3GPP and NIST guide the path strongly. The EU Cybersecurity Act builds more structure and balance. Standards create shared ground and alignment across industries. They stop chaos from spreading between networks under stress. Following them means learning from others and building resilience.
How Are Governments and Telecoms Working Together?
They share intelligence and align their goals. They test systems and verify resilience through collaboration. They write policies that cross borders and maintain safety. No single group can guard the whole field alone. Cooperation is not a choice anymore, it is survival by practice.
How Can IoT Devices Be Made More Secure?
Security must start at birth and design. Design must include encryption that protects deeply. Updates must remain automatic and timely without gaps. Devices must refuse unsafe commands under stress. The idea is not to block everything always, but to trust nothing without proof and verification.
What Role Do Encryption and Firmware Updates Play?
Encryption locks the language of data securely. Firmware updates heal the wounds that time reveals constantly. Together, they keep devices awake and honest throughout life. Ignoring either one invites decay and failure. Good maintenance keeps networks alive and trustworthy.
What’s Next for 5G Security?
Can AI and Blockchain Strengthen 5G Defenses?
AI brings awareness and speed to security. Blockchain brings trust and transparency to data control. AI learns patterns and warns early when risk rises. Blockchain records the truth that cannot be changed or denied. Together, they add strength where human limits end and fade.
What Lessons Will Shape the Move Toward 6G?
The next step will remember the scars learned. It will carry lessons from each breach and mistake. Hardware will need verification before integration. Supply chains will need clean proof throughout every stage. 6G will rise on the patience 5G teaches now with effort.
Final Thoughts
Why Is 5G Both a Revolution and a Risk?
5G feels like progress and a challenge combined. Progress is never gentle when it expands fast. The same force that connects us can expose us clearly. The same speed that drives growth can invite fall easily. Security must stand as an equal partner to innovation, not an afterthought.
How Can Collaboration Build a Safer 5G Future?
Safety needs unity and shared intention across sectors. Governments must listen to industry with respect and focus. Developers must share truth, not pride or silence. Users must learn care through awareness and choice. Together, we create a shield made of awareness and action that lasts. The future will not slow, but we can learn to walk with it and hold pace.
Views (8)
Comments (0)
Duration (0)



.jpeg)


Comments (0)
Write a Comment